Problem:
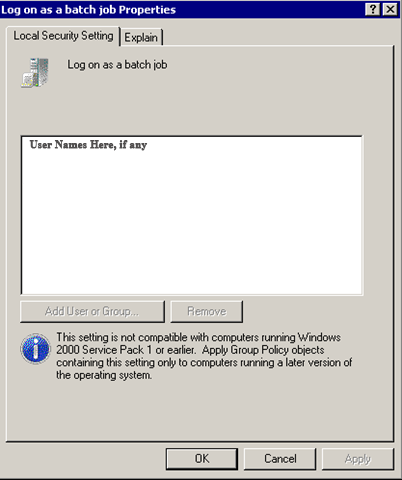
A specific domain user needs rights to run daily tasks on a specific machine. The security settings under local security policy is not allowing “Log On as Batch Job” to add a user or group.
Important Commands:
gpedit.msc (local) gpmc.msc (global) and secpol.msc
Procedure:
On the domain controller, open gpmc.msc and locate the default domain policy. Right click and edit.
Drill down through the various options as follows:
Computer Configuration – Policies – Windows Settings – Security Settings – Local Policies – User Rights
Find Log On as a Batch Job and double click.
Checkmark Define Policy, then click Add.
Click Browse, which opens a screen with check names, where you should be able to insert the user or group needed.
Possible Issues:
The Log on as a batch job user right actually presents a low-risk vulnerability that allows non-administrators to perform administrator-like functions. If not assessed, understood, and restricted accordingly, attackers could exploit this potential attack vector to compromise systems, credentials, and data. For most organizations, the default settings are sufficient. Members of the local Administrators group have this right by default.
If you configure the Log on as a batch job setting by using domain-based Group Policy settings, the computer can’t assign the user right to accounts that are used for scheduled jobs in the Task Scheduler.
So, what’s this all about, then?
As part of my own self-education in my new role as system administrator, I’ve been writing down descriptions of situations that I run into from time to time. This helps me to remember things and I thought I might pass this along to you.
Keep your curiosity alive, and stay tuned for more!